The Gap No One Talks About
Your cloud architecture is drifting — whether you realize it or not.
Over the past year, we've reviewed dozens of complex cloud environments alongside security teams. One issue surfaces almost every time: architectural drift.
It's not negligence. It's not malice. It's the natural outcome of speed, complexity, and the absence of continuous visibility.
Teams design with intention:
- Web tier isolated from the data tier
- Strict routing through inspection points
- Dev and Prod fully air-gapped
But by the time the environment is live and evolving, the reality on the ground looks very different:
→ Web load balancers end up deployed in database subnets
→ Security groups quietly accumulate rules that allow cross-environment CIDRs
→ Traffic bypasses inspection points entirely
No one planned for this. But it happens — and it's happening in your environment right now !
These Aren't Just Design Inconsistencies. They're Risk Multipliers.
- Sensitive assets get exposed through unintended paths. A Web load balancer sitting in a database subnet creates a direct route between internet-facing traffic and your most critical data: a path that was never supposed to exist. It doesn't show up as an alert. It just quietly sits there, waiting.
- Lateral movement risk increases dramatically. When Dev and Prod share connectivity through an overlooked security group rule, a compromised workload in development becomes a stepping stone into production. Attackers don't necessarily need a zero-day. They just follow the path you accidentally left open.
Why Manual Audits Can't Close This Gap
The traditional response to architectural drift is the periodic security audit: pull thousands of security group rules, compare them against design documents, try to identify what's changed, or manually reconstructing topology by crawling subnets, ENIs, route tables, and peering connections. At any meaningful scale, both break down:
- The rule review produces thousands of entries with no way to know which are active or what traffic is actually flowing through them
- The manual network map is outdated the moment you finish building it
The more fundamental problem: audits compare configurations against documentation. But documentation reflects intent, not ground truth. What you need to see is what traffic is actually flowing, and where the actual communication paths diverge from the design continuously, not on a schedule.
CSPM and CNAPP: They See Resources, Not Relationships
CSPM and CNAPP platforms are valuable, but they're built to catch misconfiguration, not architecture. They evaluate resources in isolation against compliance benchmarks. What they can't see is the structural relationship between resources and that's exactly where architectural drift lives.
Examples they'll miss entirely:
- A load balancer deployed in a database subnet - no rule violated, no benchmark failed, but internet-facing traffic now has a direct path to your data tier
- A security group quietly allowing preprod CIDRs to reach prod - each rule looks permissible in isolation, but the cross-environment path should never exist
- A workload bypassing an inspection point.
None of the above triggers a CSPM /CNAPP alert. None fail a compliance check. They're invisible to posture scanners because posture scanners don't reason about design intent, they reason about individual resource configurations.
Traditional Network Security: Rules Without Architectural Context
Firewalls and network ACLs enforce what you told them to enforce. They ask: does this connection match an allow rule? They don't ask: should this connection exist at all, given how this environment was designed?
The gap between architectural intent and live reality lives in a layer that rules-based tools were never built to see.
What Continuous Verification Actually Requires
Closing the architecture-versus-reality gap isn't about adding more scanning tools. It requires a different model entirely: one built around three capabilities that most environments are missing today:
1. A live map of actual topology and traffic
A real-time picture of which workloads are communicating, through which subnets, across which paths, built from actual network signals, not from what your IaC templates say should be there.
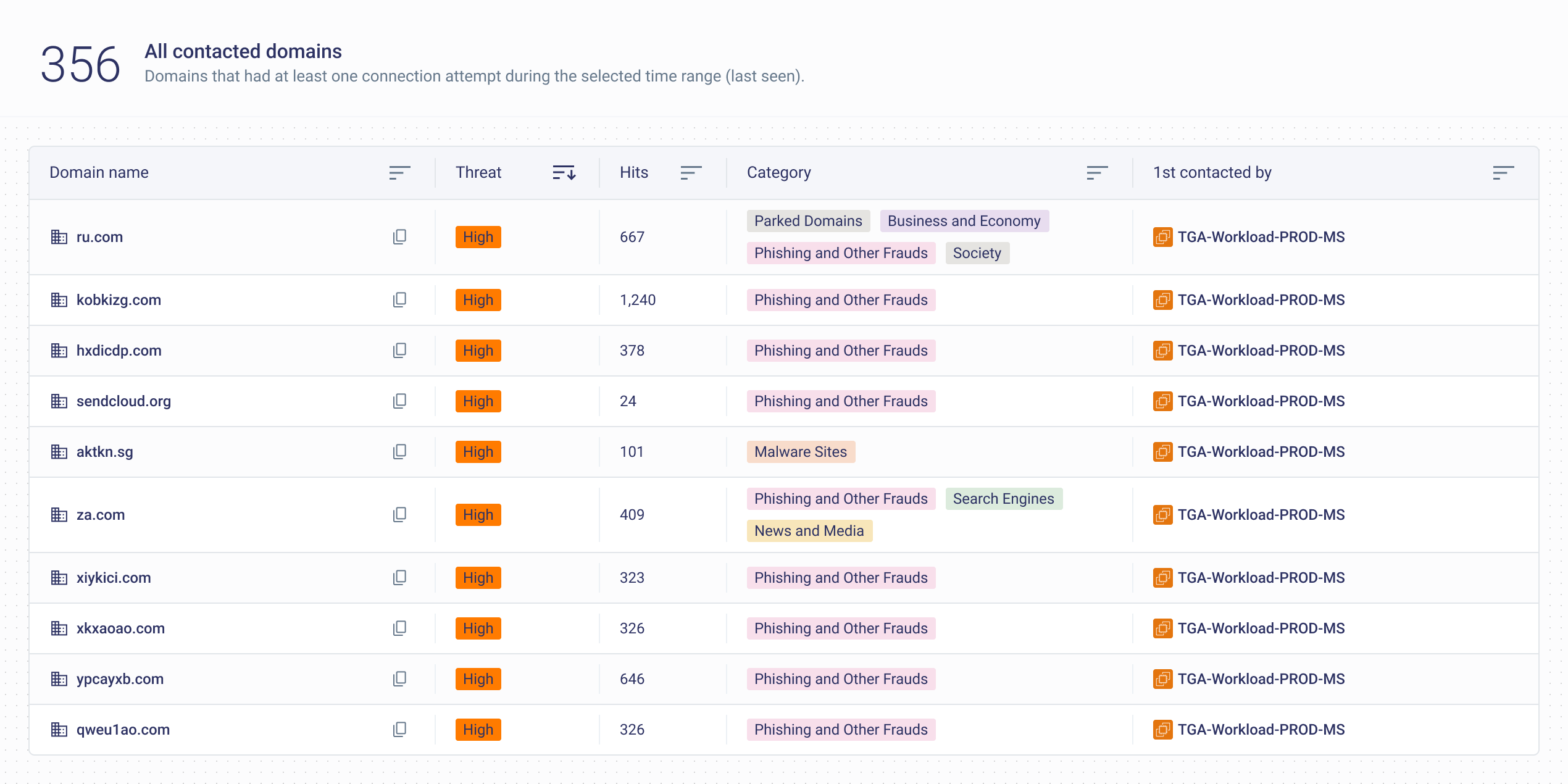
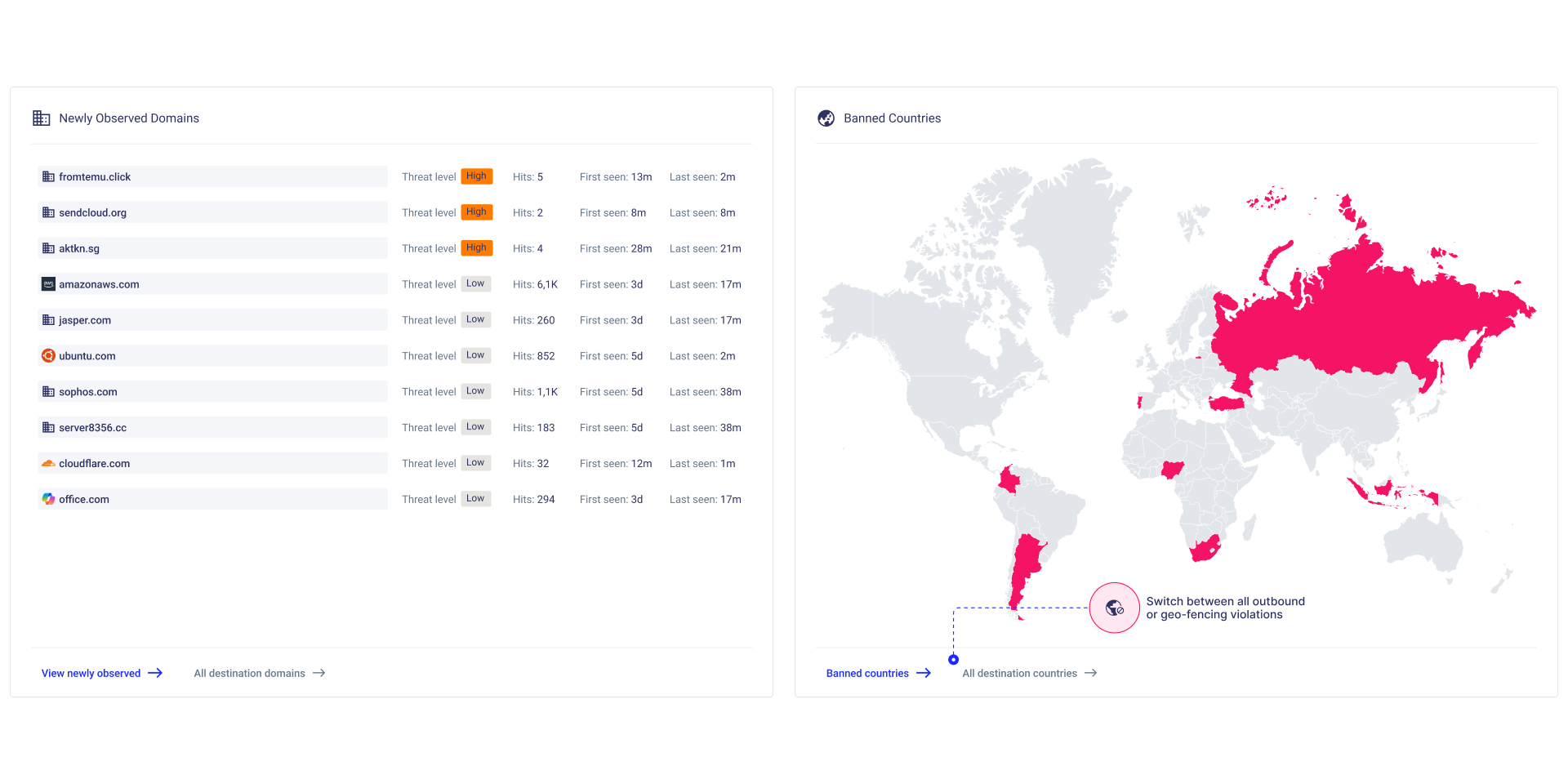
This means ingesting the signals your cloud already generates: Flow Logs, DNS query logs, resource metadata and turning them into a continuously updated picture of ground truth.
2. Guardrails that encode design intent and enforce it continuously
Security teams should be able to translate architectural decisions directly into verifiable rules: no load balancer in a database subnet. Dev and Prod never communicate directly. All outbound traffic routes through an inspection point.
These rules run continuously against the live state of the environment.
3. Instant alerting, not periodic reporting
The moment a guardrail is breached — a workload in the wrong subnet, a security group rule opening an unintended path, traffic bypassing an inspection layer — the team knows. Not next quarter. Not after the next pentest. The moment it happens.
Conclusion
The gap between your architecture diagrams and your live cloud environment isn't a failure of intent. It's a failure of visibility.
Teams that close this gap don't do it with more audits or more rules, they do it by making ground truth visible in real time, continuously and by building the ability to know the instant their architecture stops matching their design.
Want to see what your cloud actually looks like right now and where it's drifted from your design? Get a Demo
Watch a Demo
Discover how CloudFence's AI-driven engine establishes behavioral baselines, delivers real-time visibility, and detects threats before they escalate—helping your team shift from reactive firefighting to strategic cloud security management.
Stop Being in the Dark!
Watch a Demo
Discover how CloudFence's AI-driven engine establishes behavioral baselines, delivers real-time visibility, and detects threats before they escalate—helping your team shift from reactive firefighting to strategic cloud security management.
Keep Exploring Cloud Security Insights
Looking to dive deeper? Check out these handpicked articles related to cloud visibility, threat detection, and workload protection.